
[ad_1]
As the adoption of cloud computing continues to accelerate, cloud cybersecurity has become a top priority for security leaders. The benefits of moving to the cloud are clear: scalability, flexibility, and cost-savings. But the security challenges can be equally significant. CISOs must navigate a complex landscape of shared responsibility models, evolving threats, and rapidly changing compliance requirements.
One of the key concerns today is the misconfiguration of cloud services, which can expose sensitive data and systems to unauthorized access. In fact, a Dark Reading report found that 65% of cloud security incidents are caused by customer misconfiguration, mismanagement, and mistakes. CISOs must ensure their teams have the necessary skills and processes in place to properly configure cloud infrastructure and maintain secure deployments.
Another major challenge is the proliferation of cloud-based applications and the need to manage identities and access across a distributed environment. With employees accessing cloud services from various devices and locations, traditional perimeter-based security models are no longer sufficient. CISOs must implement robust identity and access management (IAM) controls, including multi-factor authentication, to verify user identities and limit access to only what is necessary.
Compliance is also a significant hurdle for organizations operating in the cloud. Regulatory frameworks like GDPR, HIPAA, and PCI-DSS have specific requirements for data protection and security controls that must be met, even when leveraging cloud infrastructure. CISOs need to carefully assess the compliance posture of their cloud providers and ensure their own cloud deployments adhere to the necessary standards.
To address these challenges, CISOs should take a proactive, multi-layered approach to cloud security. This includes:
- Establishing clear cloud security governance and policies to guide the organization’s cloud adoption and usage. This involves defining roles and responsibilities, setting security baselines, and aligning cloud security with broader enterprise risk management strategies.
- Implementing robust cloud security monitoring and incident response capabilities to detect and respond to threats. This may involve leveraging cloud-native security tools, integrating with existing security operations, and establishing clear incident response playbooks for cloud-related incidents.
- Leveraging cloud-native security tools and services to automate security controls and maintain continuous compliance. This can include features like automated configuration management, continuous vulnerability scanning, and cloud security posture management.
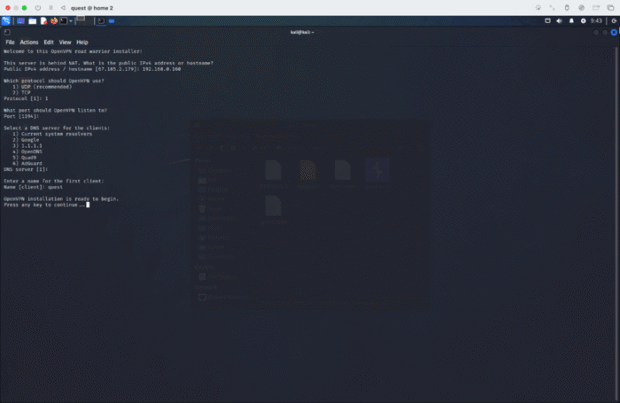
- Conducting regular cloud penetration testing and security assessments to identify and address vulnerabilities in the cloud environment. This should include both technical testing and evaluations of cloud security controls and processes.
- Fostering a culture of cloud security awareness and training among all employees to mitigate the risk of human error. This includes educating users on cloud security best practices, secure cloud application usage, and incident reporting procedures.
- Developing comprehensive cyber crisis management plans to ensure the organization is prepared to respond effectively to cloud-related security incidents and data breaches. This should include incident escalation procedures, communication protocols, and business continuity strategies specific to the cloud environment.
By addressing these critical cloud security considerations, CISOs can empower their organizations to securely harness the power of cloud computing and drive digital transformation initiatives forward.
[ad_2]
Source link








Be the first to leave a comment